White Papers
-
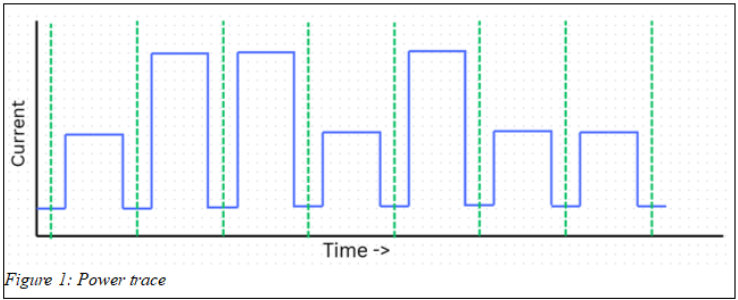
Hardware Attacks: Glitching and More
Introduction Hardware attacks are a class of exploits that rely on the way that processors act in the…
-
AI in Cyber Security: Offensive vs Defensive
Introduction The integration of Artificial Intelligence (AI) into the digital world has fundamentally altered Cyber Security. Over the…
-
Polyglots: A Chameleon’s Best Friend
Introduction What are polyglots? Polyglots in a security context; are files which can be interpreted as multiple valid…
-
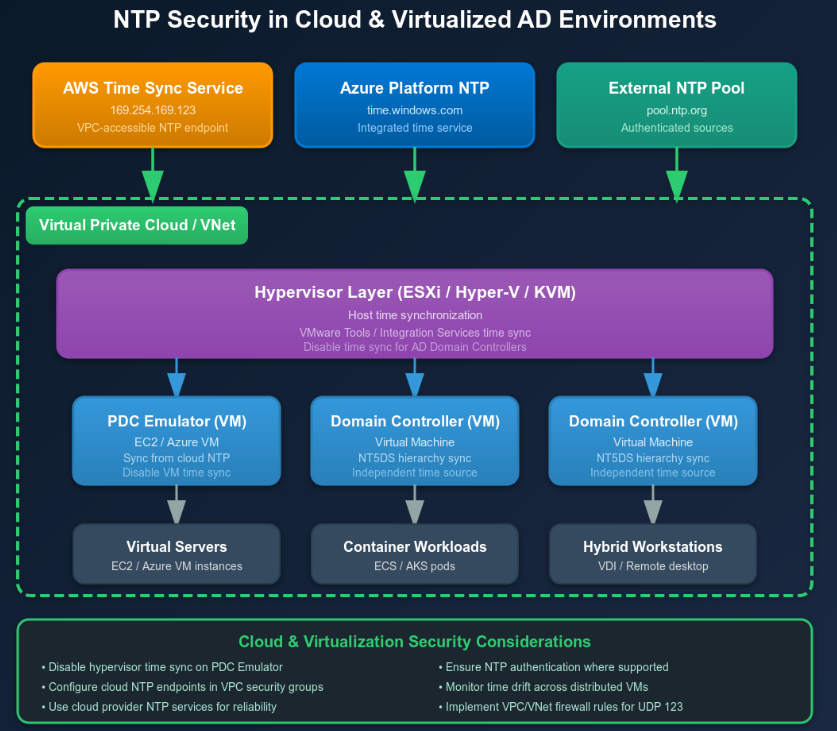
Timeroasting: An Introduction to NTP Hacking
Introduction Timeroasting is a classification of attack which targets a system’s management of time. Compared to other categories…
-
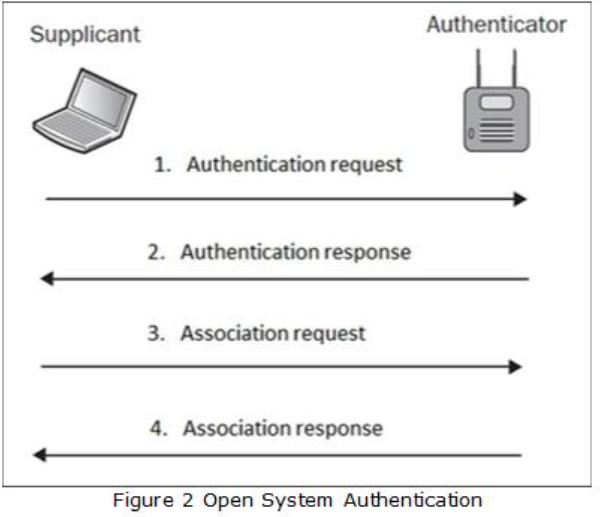
Wireless Network Vulnerabilities: An Introduction to Wi-Fi Hacking
Introduction to Wi-Fi Wi-Fi is a wireless network technology that allows devices to connect to the internet and…
-
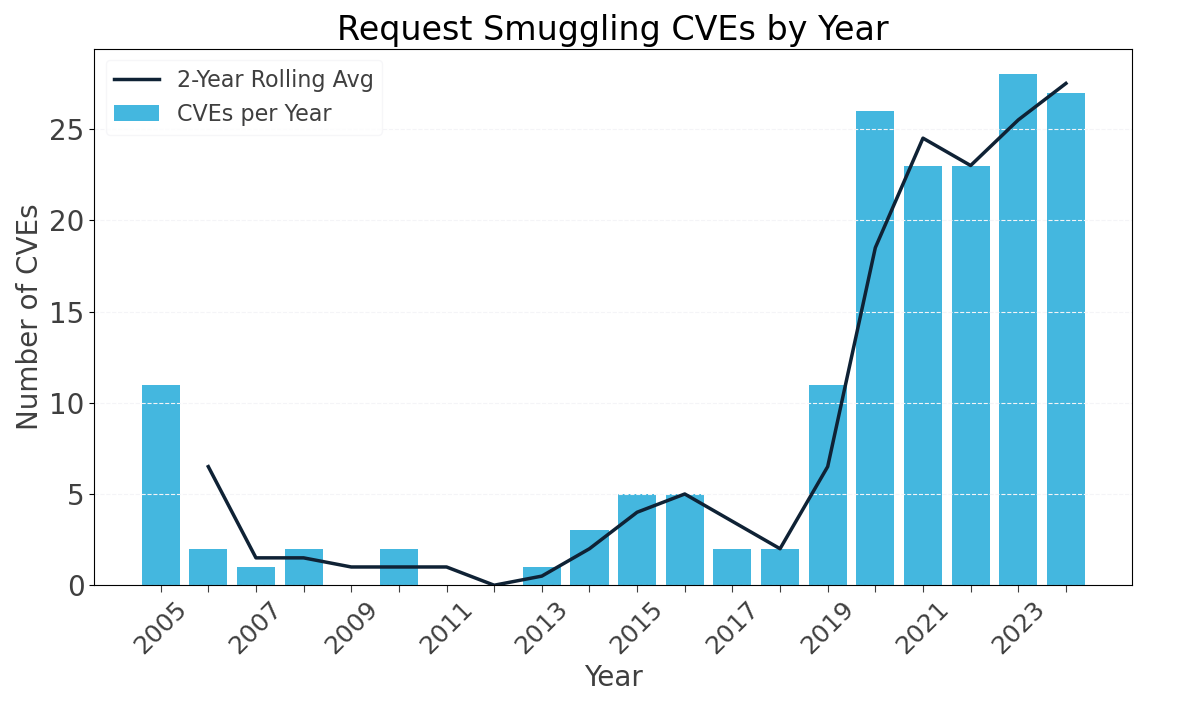
HTTP Request Smuggling: From RFC to Real-World Impact
Introduction HTTP request smuggling is a web application vulnerability that leverages discrepancies and ambiguity in how frontend and…
-
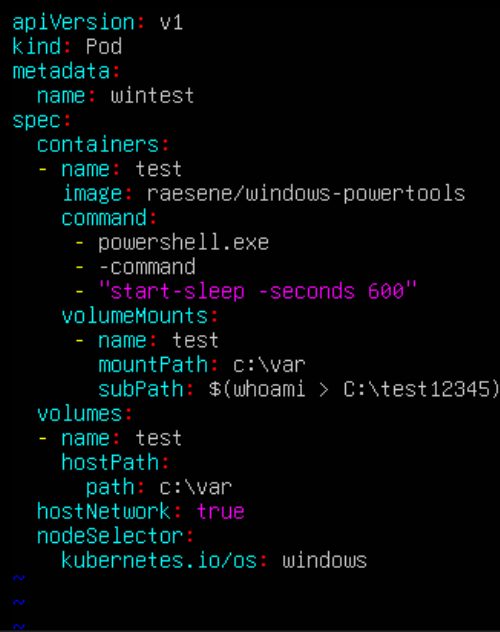
Kubernetes Volumes: Command Injection Heaven
Introduction Kubernetes, the automation and containerisation platform, has a function for sharing files between nodes and pods named…
-
CUPS: Exploring the Recent RCE
Introduction On the 26th of September 2024, Simone Margaritelli, also known as ‘Evilsocket’ disclosed, publicly, four vulnerabilities within…
-
Common Vulnerabilities in Kubernetes
Introduction to Kubernetes Kubernetes is an open-source platform used for automating the deployment and management of containerised applications….